Hardware and Software Specifications, Examples, Links, and other info. are valid at the publishing time. In case it become invalid use the Internet Search.
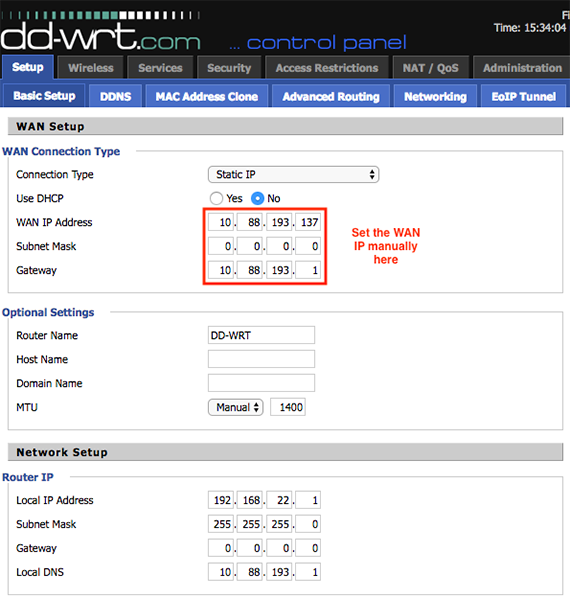
Aug 08, 2015 Finding Public/WAN IP address on a router. A few ADSL/Cable router allows you to login to your router using telnet or ssh: telnet your-router-ip-here ssh user@your-router-ip-here telnet 192.168.0.254 ssh admin@192.168.1.254 admin@dd-wrt # ifconfig eth1 grep 'inet addr:' admin@dd-wrt # ip addr show nas01 Use 3rd party web-sites to get.
- Config rule 'examplemailwan' option destip '62.254.26.219' option family 'ipv4' option usepolicy 'wanonly' This is the IP of smtp.virginmedia.com, you may need to add more IP addresses in order to cover IMAP, POP3 and other SMTP servers if used. You could also add use the proto and destport on rules to limit it to mail related ports.
- Your WAN IP Information. IP Address: 207.46.13.86. Host: msnbot-207-46-13-86.search.msn.com. Welcome to IPmotivation! Free Tools for WAN IP Address properties and Reverse DNS Lookup. Copyright (c) 2011-2013 Keith Ness & Associates.
- May 01, 2021 config rule 'examplemailwan' option destip '62.254.26.219' option family 'ipv4' option usepolicy 'wanonly' This is the IP of smtp.virginmedia.com, you may need to add more IP addresses in order to cover IMAP, POP3 and other SMTP servers if used. You could also add use the proto and destport on rules to limit it to mail related ports.
1st Published, Dec. 2004
Over 6,500,000 Hits Site Wide in 2006
Connecting through the Internet to a Home / SOHO Computer / Server. Or How Do I find My Network on the Internet?
In order to log to an Internet site/server you need a valid address. Such an address might be the IP number (like http://207.46.250.222), a name like www.ezlan.net or http://jack.dns-ip.com
This page will describe few options to enable you to use any Internet connection in the world to connect to your Home/SOHO Network/Server.
Your system has to be prepared to accept a connection from the outside.
If the Serving system is behind a Router or and Firewall the Ports that are associated with the serving applications have to be opened through both Firewalls. (Opening Ports).
If you would like to Remotely Control your Computers you have to install a Remote Control program.
Example: Ultr@VNC - Installation, and Settings.
If you would to run a sever and make it available through the Internet you have to configure a functional Server on one of your computers.
You can run HTTP, FTP, Email, or any other regular server, the methods describe bellow will fit all of them.
If you are Not familiar with Server installation, you might Start with some thing modest like this: Simple Server
On IPs.
When using Internet connection and LAN in a regular home setting, there are two kinds of IP Numbers that are assigned to your Network..
1. External IP (WAN IP). This is the IP that your ISP assigns to you to use the Internet.
2. Internal IP (LAN IP). This is the IPs assigned to your LAN's computers (the 192.168.xxx.xxx type).
If you need more info about IPs and How to find them.
To connect to your Computer/Server from the outside there is a need to know your External IP Address.
Option 1 - Static IP.
If you have a static IP it is very simple since your External IP number is always the same. Any one can connect to your system, all they have to do is to type your IP number into their Internet Browser Address Bar. Example: http://168.143.107.163
Let recap. I have a static WAN IP (fake example): http://168.143.107.163
One of my Network's computer at home run Simple server with files as described in the Simple Server link above. I am in my hotel in Vegas and I need a file.
I connect my Laptop to the Hotel's Internet connection. I start the Browser (I.E.) and type into the address bar http://168.143.107.163 that it, if set correctly my I will see my files on the screen.
Unfortunately, almost all low cost Broadband Internet connections are Dynamic. I.e. they change often according to the ISP preferences.
Option 2 - Email me my valid IP address.
If you just want to contact your computer by yourself and you have an access to your email from any place with Internet connection.
Get this free program. This nice program would email your Network/Server Current External IP to an email address of your choice: dynamicIP
Install it on one of your computers, and it will periodically send an email to your email address telling you what is the current External IP. Type the IP to the address bar of any Internet connection in the world and you will get to your system (provided you Opened the Ports to the specific Computer through your Firewalls, and left the system running).
Let recap this One. My Internet Connection WAN IP is of the dynamic type. I set dynamicIP program to check every 10 minutes email to my WebMail address (example: jack@gmail.com) if the number changed from the previous reading.
I am in my hotel in Vegas and I need a file that is residing on my office server. I log to the Internet, I log to my Gmail account, I see the email with my current WAN IP.
I copy IP number, and paste it to the Browser (I.E.) address bar. If set correctly I would see the files that are on my home server and would be able to download the file of my choice.
Option 3 - Dynamic DNS Service.
You do not want to be bothered with the above email process, and or you would like to make your Computer/Server/Network to be available through the Internet.
Use a DNS Service.
DNS= Domain Name Servers are Data Bases spread all over the Internet telling the system what is the current address of the server that you are Trying to reach.
The DNS services would provide you with personal service to Route your Dynamic address to a permanent presence on the Internet.
These services (some of them are Free) will provide you with a small Client program that should be installed on your server computer. This program will detect changes in your WAN IP and would automatically send the current External IP to the DNS Service.
When someone wants to connect to your server and use your Internet address they actually connect to your permanent personal address with the DNS service, and the service redirect the traffic to your current IP of your Internet connection.
Example: I subscribed to the Free DNS service myip.us as 'jack'. My assigned Internet address would be http://jack.myip.us (notice no www since jack is sub domain of www.myip.us).
Given this setting my Home Server can be reached from every place on the Internet by typing into the Browser Address Bar: http://jack.myip.us
Here is a list of most free (and for pay) DNS Services.
The important aspects of the table in the link bellow are the first two columns.
Link to: List of DNS Services.
Column 1 - Sub Domains. It means that you do not have to buy any Internet Domain (as an example www.ezlan.net is a name of a domain). Your Domain becomes a sub domain of the service.
Example: If you subscribe to the DNS service www.myip.us as 'jack' your Internet address would be http://jack.myip.us (notice no www since it is sub domain of www.myip.us).
Column 2 - Custom Domain. The DNS service might be free but it requires you to buy a Domain before you start to use the service. The cost of a Domain is about $7-$15 per year.
When using Custom Domain, the DNS service will provide the redirection service but your Internet address will be your domain. I.e. if you bought the Domain www.jack.com any one who types www.jack.com into their browser will be Routed to your Server.
If you buy a Domain make sure that it is actually yours and that you can host the domain on any server of your choice.
Some inexpensive domain vendors make their income from insisting that your Web Site has to be on their fee for service Hosting system and you have to pay Extra if you move your Web Site to be Hosted by another vendor.
Do not buy a Domain that does not provide you with On Line Domain Controller.
If there is No online Domain Controller you are at the merci of the support practice of the Domain Vendor.
What is a Domain Controller?
It is a link to a page in the site of your Domain Vendor that allows you (with an adequate password) to control on line all the aspects involving your domain
Including, Ownership, Hosting DNS, etc.
Since it is available Online you do not need to contact the vendor's support system to make changes to your domain settings.
Check your contract with your ISP running certain type of servers might be a violation of you Term of Service (TOS).
Copyright © 2001-2007 EZLAN.NET. All Rights Reserved.
Home
Important
NAT rules are currently in public preview.This preview version is provided without a service level agreement and it's not recommended for production workloads. Certain features might not be supported or might have constrained capabilities.For more information, see Supplemental Terms of Use for Microsoft Azure Previews.
You can configure your Virtual WAN VPN gateway with static one-to-one NAT rules. A NAT rule provides a mechanism to set up one-to-one translation of IP addresses. NAT can be used to interconnect two IP networks that have incompatible or overlapping IP addresses. A typical scenario is branches with overlapping IPs that want to access Azure VNet resources.
This configuration uses a flow table to route traffic from an external (host) IP Address to an internal IP address associated with an endpoint inside a virtual network (virtual machine, computer, container, etc.).
Configure NAT rules
You can configure and view NAT rules on your VPN gateway settings at any time.
Navigate to your virtual hub.
Select VPN (Site to site).
Select NAT rules (Edit).
On the Edit NAT Rule page, you can Add/Edit/Delete a NAT rule using the following values:
- Name: A unique name for your NAT rule.
- Type: Static. Static one-to-one NAT establishes a one-to-one relationship between an internal address and an external address.
- Mode: IngressSnat or EgressSnat.
- IngressSnat mode (also known as Ingress Source NAT) is applicable to traffic entering the Azure hub's Site-to-site VPN gateway.
- EgressSnat mode (also known as Egress Source NAT) is applicable to traffic leaving the Azure hub's Site-to-site VPN gateway.
- InternalMapping: An address prefix range of source IPs on the inside network that will be mapped to a set of external IPs. In other words, your pre-NAT address prefix range.
- ExternalMapping: An address prefix range of destination IPs on the outside network that source IPs will be mapped to. In other words, your post-NAT address prefix range.
- Link Connection: Connection resource that virtually connects a VPN site to the Azure hub's Site-to-site VPN gateway.
Configuration considerations
- The subnet size for both internal and external mapping must be the same for static one-to-one NAT.
- Be sure to edit the VPN site in the Azure portal to add ExternalMapping prefixes in the 'Private Address Space' field. Currently, sites that have BGP enabled need to ensure that the on-premises BGP announcer (device BGP settings) include an entry for the external mapping prefixes.
Examples and verification
Ingress mode NAT
Ingress mode NAT rules are applied on packets that are entering Azure through the Virtual WAN Site-to-site VPN gateway. In this scenario, you want to connect two Site-to-site VPN branches to Azure. VPN Site 1 connects via Link1, and VPN Site 2 connects via Link 2. Each site has the address space 192.169.1.0/24.
The following diagram shows the projected end result:
Specify a NAT rule.
Specify a NAT rule to ensure the Site-to-site VPN gateway is able to distinguish between the two branches with overlapping address spaces (such as 192.168.1.0/24). In this example, we focus on Link1 for VPN Site 1.
The following NAT rule can be set up and associated to Link 1 of one of the branches. Because this is a static NAT rule, the address spaces of the InternalMapping and ExternalMapping contain the same number of IP addresses.
- Name: IngressRule01
- Type: Static
- Mode: IngressSnat
- InternalMapping: 192.168.1.0/24
- ExternalMapping: 10.1.1.0/24
- Link Connection: Link 1
Advertise the correct ExternalMapping.
In this step, ensure that your Site-to-site VPN gateway advertises the correct ExternalMapping address space to the rest of your Azure resources. There are different instructions, depending on whether BGP is enabled, or not.
Example 1: BGP is enabled
- Ensure that the on-premises BGP speaker located at VPN Site 1 is configured to advertise the 10.1.1.0/24 address space.
- During this preview, sites that have BGP enabled need to ensure that the on-premises BGP announcer (device BGP settings) include an entry for the external mapping prefixes.
Example 2: BGP is not enabled
Navigate to the Virtual hub resource that contains the Site-to-site VPN gateway. On the virtual hub page, under Connectivity, select VPN (Site-to-site).
Select the VPN site that is connected to the Virtual WAN hub via Link 1. Select Edit Site and input 10.1.1.0/24 as the private address space for the VPN site.
Packet flow
In this example, an on-premises device wants to reach a spoke virtual network. The packet flow is as follows, with the NAT translations in bold.
- Traffic from on-premises is initiated.
- Source IP Address: 192.168.1.1
- Destination IP Address: 30.0.0.1
- Traffic enters Site-to-site gateway and is translated using the NAT rule and then sent to the Spoke.
- Source IP Address: 10.1.1.1
- Destination IP Address: 30.0.0.1
- Reply from Spoke is initiated.
- Source IP Address: 30.0.0.1
- Destination IP Address: 10.1.1.1
- Traffic enters the Site-to-site VPN gateway and the translation is reversed and sent to on-premises.
- Source IP Address: 30.0.0.1
- Destination IP Address: 192.168.1.1
Verification checks
This section shows checks to verify that your configuration is set up properly.
Validate DefaultRouteTable, rules, and routes
Branches in Virtual WAN associate to the DefaultRouteTable, implying all branch connections learn routes that are populated within the DefaultRouteTable. You will see the NAT rule with the external mapping prefix in the effective routes of the DefaultRouteTable.
Example:
- Prefix: 10.1.1.0/24
- Next Hop Type: VPN_S2S_Gateway
- Next Hop: VPN_S2S_Gateway Resource
Validate address prefixes
This example applies to resources in virtual networks that are associated to the DefaultRouteTable.
The Effective Routes on the Network Interface Cards (NIC) of any virtual machine that is sitting in a Spoke virtual network connected to the Virtual WAN hub should also contain the address prefixes of the NAT rules ExternalMapping.
Validate BGP advertisements
Dyndns Login
If you have BGP configured on the VPN site connection, check the on-premises BGP speaker to make sure it is advertising an entry for the external mapping prefixes.
Next steps
What Is My Wan Ip

Given this setting my Home Server can be reached from every place on the Internet by typing into the Browser Address Bar: http://jack.myip.us
Here is a list of most free (and for pay) DNS Services.
The important aspects of the table in the link bellow are the first two columns.
Link to: List of DNS Services.
Column 1 - Sub Domains. It means that you do not have to buy any Internet Domain (as an example www.ezlan.net is a name of a domain). Your Domain becomes a sub domain of the service.
Example: If you subscribe to the DNS service www.myip.us as 'jack' your Internet address would be http://jack.myip.us (notice no www since it is sub domain of www.myip.us).
Column 2 - Custom Domain. The DNS service might be free but it requires you to buy a Domain before you start to use the service. The cost of a Domain is about $7-$15 per year.
When using Custom Domain, the DNS service will provide the redirection service but your Internet address will be your domain. I.e. if you bought the Domain www.jack.com any one who types www.jack.com into their browser will be Routed to your Server.
If you buy a Domain make sure that it is actually yours and that you can host the domain on any server of your choice.
Some inexpensive domain vendors make their income from insisting that your Web Site has to be on their fee for service Hosting system and you have to pay Extra if you move your Web Site to be Hosted by another vendor.
Do not buy a Domain that does not provide you with On Line Domain Controller.
If there is No online Domain Controller you are at the merci of the support practice of the Domain Vendor.
What is a Domain Controller?
It is a link to a page in the site of your Domain Vendor that allows you (with an adequate password) to control on line all the aspects involving your domain
Including, Ownership, Hosting DNS, etc.
Since it is available Online you do not need to contact the vendor's support system to make changes to your domain settings.
Check your contract with your ISP running certain type of servers might be a violation of you Term of Service (TOS).
Copyright © 2001-2007 EZLAN.NET. All Rights Reserved.
Home
Important
NAT rules are currently in public preview.This preview version is provided without a service level agreement and it's not recommended for production workloads. Certain features might not be supported or might have constrained capabilities.For more information, see Supplemental Terms of Use for Microsoft Azure Previews.
You can configure your Virtual WAN VPN gateway with static one-to-one NAT rules. A NAT rule provides a mechanism to set up one-to-one translation of IP addresses. NAT can be used to interconnect two IP networks that have incompatible or overlapping IP addresses. A typical scenario is branches with overlapping IPs that want to access Azure VNet resources.
This configuration uses a flow table to route traffic from an external (host) IP Address to an internal IP address associated with an endpoint inside a virtual network (virtual machine, computer, container, etc.).
Configure NAT rules
You can configure and view NAT rules on your VPN gateway settings at any time.
Navigate to your virtual hub.
Select VPN (Site to site).
Select NAT rules (Edit).
On the Edit NAT Rule page, you can Add/Edit/Delete a NAT rule using the following values:
- Name: A unique name for your NAT rule.
- Type: Static. Static one-to-one NAT establishes a one-to-one relationship between an internal address and an external address.
- Mode: IngressSnat or EgressSnat.
- IngressSnat mode (also known as Ingress Source NAT) is applicable to traffic entering the Azure hub's Site-to-site VPN gateway.
- EgressSnat mode (also known as Egress Source NAT) is applicable to traffic leaving the Azure hub's Site-to-site VPN gateway.
- InternalMapping: An address prefix range of source IPs on the inside network that will be mapped to a set of external IPs. In other words, your pre-NAT address prefix range.
- ExternalMapping: An address prefix range of destination IPs on the outside network that source IPs will be mapped to. In other words, your post-NAT address prefix range.
- Link Connection: Connection resource that virtually connects a VPN site to the Azure hub's Site-to-site VPN gateway.
Configuration considerations
- The subnet size for both internal and external mapping must be the same for static one-to-one NAT.
- Be sure to edit the VPN site in the Azure portal to add ExternalMapping prefixes in the 'Private Address Space' field. Currently, sites that have BGP enabled need to ensure that the on-premises BGP announcer (device BGP settings) include an entry for the external mapping prefixes.
Examples and verification
Ingress mode NAT
Ingress mode NAT rules are applied on packets that are entering Azure through the Virtual WAN Site-to-site VPN gateway. In this scenario, you want to connect two Site-to-site VPN branches to Azure. VPN Site 1 connects via Link1, and VPN Site 2 connects via Link 2. Each site has the address space 192.169.1.0/24.
The following diagram shows the projected end result:
Specify a NAT rule.
Specify a NAT rule to ensure the Site-to-site VPN gateway is able to distinguish between the two branches with overlapping address spaces (such as 192.168.1.0/24). In this example, we focus on Link1 for VPN Site 1.
The following NAT rule can be set up and associated to Link 1 of one of the branches. Because this is a static NAT rule, the address spaces of the InternalMapping and ExternalMapping contain the same number of IP addresses.
- Name: IngressRule01
- Type: Static
- Mode: IngressSnat
- InternalMapping: 192.168.1.0/24
- ExternalMapping: 10.1.1.0/24
- Link Connection: Link 1
Advertise the correct ExternalMapping.
In this step, ensure that your Site-to-site VPN gateway advertises the correct ExternalMapping address space to the rest of your Azure resources. There are different instructions, depending on whether BGP is enabled, or not.
Example 1: BGP is enabled
- Ensure that the on-premises BGP speaker located at VPN Site 1 is configured to advertise the 10.1.1.0/24 address space.
- During this preview, sites that have BGP enabled need to ensure that the on-premises BGP announcer (device BGP settings) include an entry for the external mapping prefixes.
Example 2: BGP is not enabled
Navigate to the Virtual hub resource that contains the Site-to-site VPN gateway. On the virtual hub page, under Connectivity, select VPN (Site-to-site).
Select the VPN site that is connected to the Virtual WAN hub via Link 1. Select Edit Site and input 10.1.1.0/24 as the private address space for the VPN site.
Packet flow
In this example, an on-premises device wants to reach a spoke virtual network. The packet flow is as follows, with the NAT translations in bold.
- Traffic from on-premises is initiated.
- Source IP Address: 192.168.1.1
- Destination IP Address: 30.0.0.1
- Traffic enters Site-to-site gateway and is translated using the NAT rule and then sent to the Spoke.
- Source IP Address: 10.1.1.1
- Destination IP Address: 30.0.0.1
- Reply from Spoke is initiated.
- Source IP Address: 30.0.0.1
- Destination IP Address: 10.1.1.1
- Traffic enters the Site-to-site VPN gateway and the translation is reversed and sent to on-premises.
- Source IP Address: 30.0.0.1
- Destination IP Address: 192.168.1.1
Verification checks
This section shows checks to verify that your configuration is set up properly.
Validate DefaultRouteTable, rules, and routes
Branches in Virtual WAN associate to the DefaultRouteTable, implying all branch connections learn routes that are populated within the DefaultRouteTable. You will see the NAT rule with the external mapping prefix in the effective routes of the DefaultRouteTable.
Example:
- Prefix: 10.1.1.0/24
- Next Hop Type: VPN_S2S_Gateway
- Next Hop: VPN_S2S_Gateway Resource
Validate address prefixes
This example applies to resources in virtual networks that are associated to the DefaultRouteTable.
The Effective Routes on the Network Interface Cards (NIC) of any virtual machine that is sitting in a Spoke virtual network connected to the Virtual WAN hub should also contain the address prefixes of the NAT rules ExternalMapping.
Validate BGP advertisements
Dyndns Login
If you have BGP configured on the VPN site connection, check the on-premises BGP speaker to make sure it is advertising an entry for the external mapping prefixes.
Next steps
What Is My Wan Ip
My Wan Ip Address
For more information about Site-to-site configurations, see Configure a Virtual WAN Site-to-site connection.

